DASCTF八月挑战赛 re#
做完了逆向,不得不说das的re还是比较友好的
py
得到文件py.exe,肯定就是考python打包成exe文件了。可以参考文章https://blog.csdn.net/m0_37552052/article/details/88093427
用pyinstxtractor.py还原
python pyinstxtractor.py [filename]
得到文件夹,看到里面有个py.pyc,直接还原不行,用文章里面的方法还原pyc头文件,如果想学习pyc还可以看看这篇文章https://zhuanlan.zhihu.com/p/145811103
得到py文件。
1 |
|
很简单
1 |
|
apkrev
简单的apk逆向,加密函数和密文都在so文件的mycheck中,有经验的话不难看出是rc4,看不出来也没关系,反正最后就是一个异或,动调把异或数组取出来就行了,动调apk方法在https://the_itach1.gitee.io/2021/08/02/D0g3%E6%AF%94%E8%B5%9B%E5%B9%B3%E5%8F%B0%20re%20wp/的medical_app。
由于比较懒,不想一个一个调,就直接输入了个错误flag,然后得到假密文,去得到异或的数组。好像rc4的key是12345678,可能也可以用rc4来做。
1 |
|
LittleJunk
好家伙,题刚出来2分钟就有人直接秒了,可能是出题人。
就是有很多花指令,来干扰分析,动调就好了,main函数前面一大部分感觉都是用来解密函数代码的,真正要看的地方在(loc_584000)(&v19);
进去可以看到,图片里面忘了说sub_581FA0应该也是用来解密函数代码的。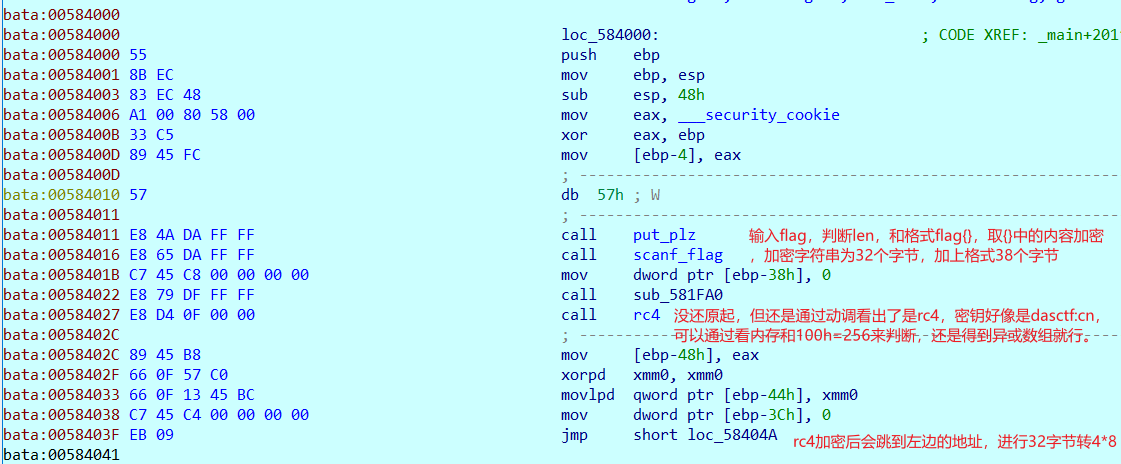
然后先看看rc4吧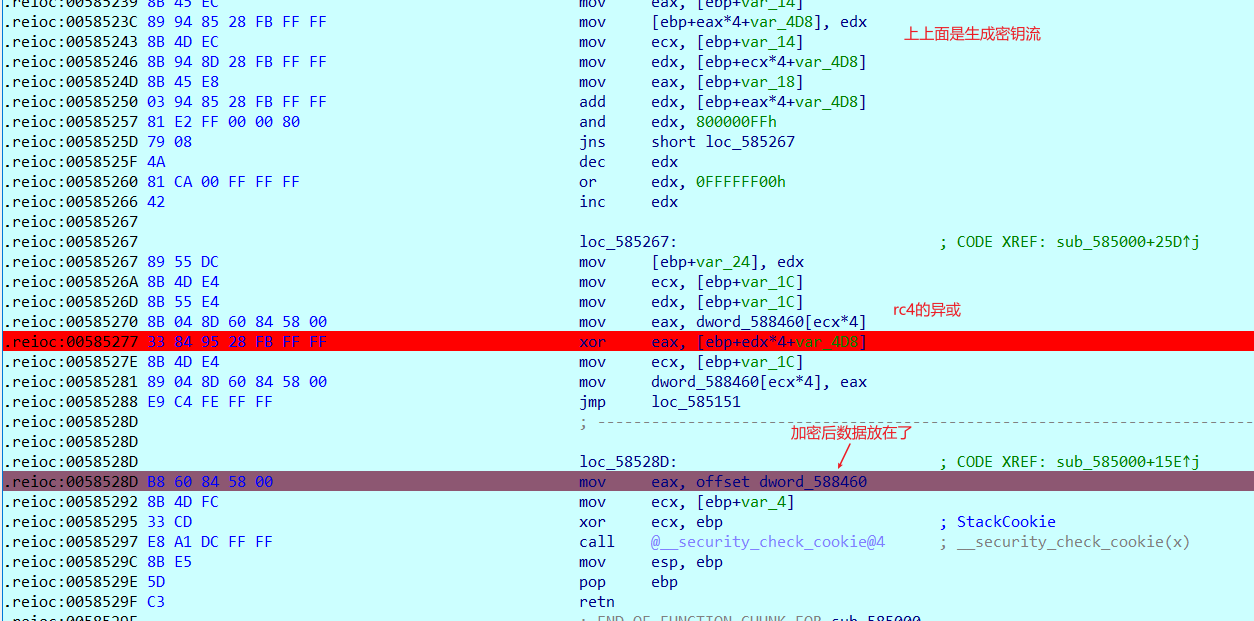
retn后,32字节转4*8
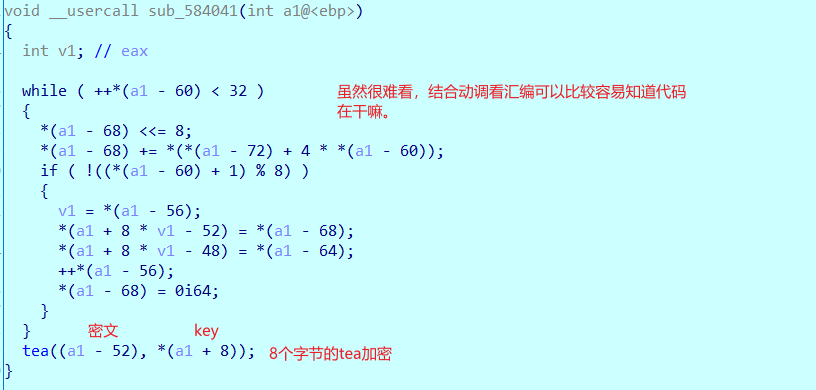
魔改的tea。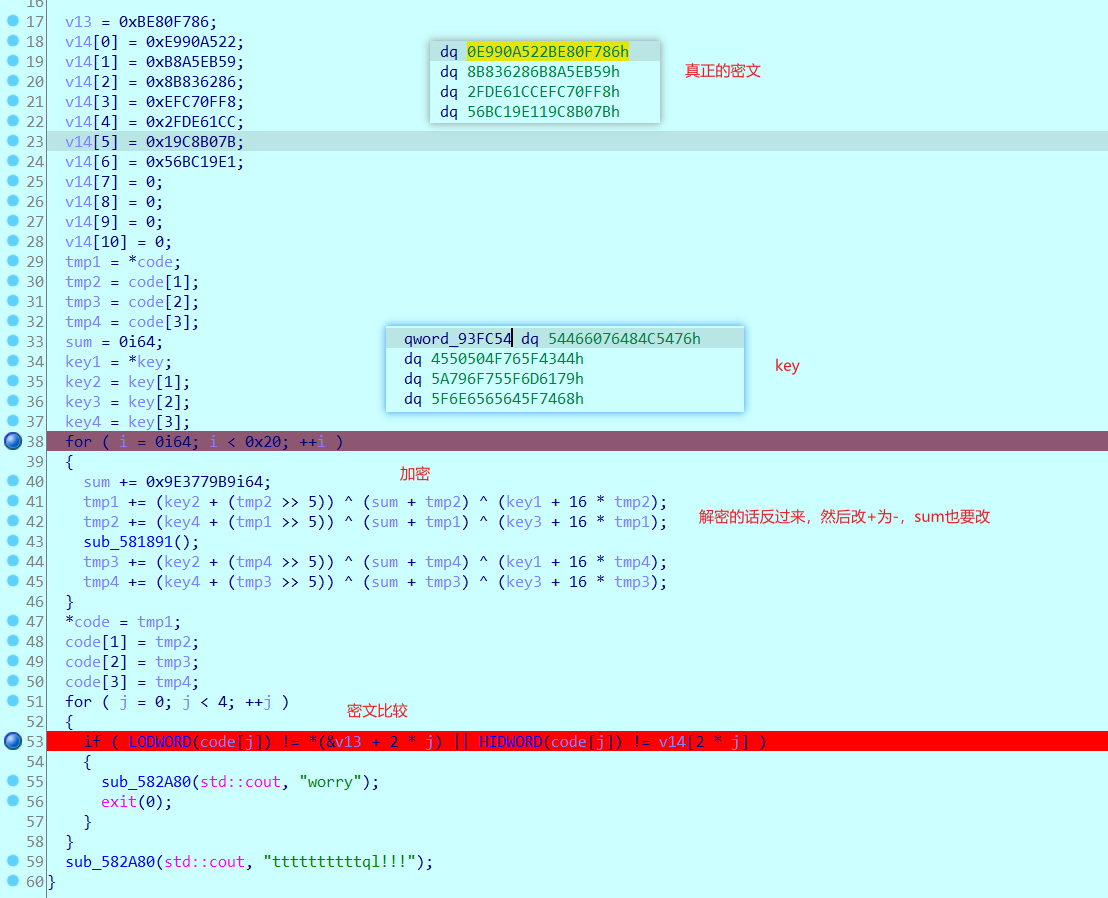
然后解密
1 |
|
1 |
|
寒王’sblog
照着博客做就行,关键是flag.jpg在哪,开始以为是头像,结果没解出来,后面f12看网页,也没找到,然后试了试直接在网页后面加上\flag.jpg,还真的有。
本人blog:https://the_itach1.gitee.io/






